Intro
Choosing the right Identity and Acess Management solution can become really hard as you dive deeper into the realm of security.
Like any other solutions, the market is full of them. However, I consider that choosing the right IAM is more about having a framework and filtering the existing solutions.
The alternative is to choose blindly and in a few months, you’ll need to migrate from one IAM to another. Do yourself a favor and let’s explore the process of choosing the right solution for your startup.
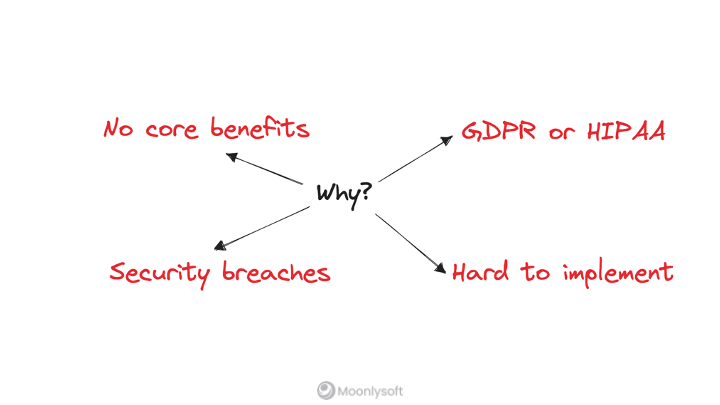
Should you implement the IAM by yourself?
I would argue that if you are not an enterprise company, then the obvious answer is No. There are a number of reasons why you wouldn’t want to implement an IAM solution by yourself
- You would have to keep up with GDPR and HIPAA compliance. That means you would need a legal team to take care of these aspects.
- Security breaches. You would need a person that constantly checks the latest security breaches and updates the system accordingly.
- And there’s the obvious: it’s hard to implement. There are tons of things you would need to consider for such a complex implementation. From architecting the system, developing it, and deploying it into a reliable infrastructure, and then there’s the maintenance part that no one will do for you.
- Above all reasons, the fact that an IAM solution is not part of your core business is the most significant reason why you shouldn’t implement one by yourself. You should be focusing on developing the features that give you leverage, the ones that attract users, not to brave with a custom-made IAM that won’t benefit the end user.
Standards
Let’s assume you decided to integrate an existing IAM solution. There are a few criteria that we’ve discovered and used whenever we had to implement such a solution.
One of them is related to Standards.
Does your potential IAM solution support all the standards you’ll use? Like SAML, OAuth2, LDAP, or OpenId Connect?
Be careful when choosing one potential solution, because it might have all the standards you need today, but does it have the ones that you might need in the future?
As a rule of thumb: The already establish IAM solutions tend to have all of the standards implemented and are already tested and validated by the market. Keep in mind that the new solutions on the market might lack some.
Migration
I would suggest keeping in mind that you might want to migrate out of the IAM you are about to use. That’s why it’s important to have the migration criteria from the beginning.
Migrating from one IAM to another IAM can be easy, especially for open-source solutions, but can also be hard. For example, Google’s Firebase Authentication is a solution that is quite hard to migrate from. They have a specific algorithm for encrypting the passwords that is not a standard one.
Fortunately, there are solutions to migrate out of an existing IAM.
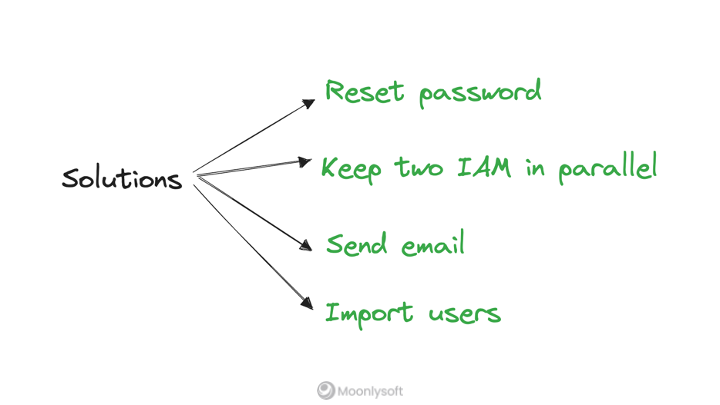
One of those is resting the password. So you managed to migrate the users from the old IAM to the new one, but the password had different encryption and are lost. Using the reset password, you can store the new password in the new IAM.
A similar thing is with sending an email. You send them an email to add a new password.
Although these are feasible solutions, I don’t necessarily like them. I don’t consider it the end user’s responsibility to “save” you and these migrations should be done behind the scenes.
Keeping two IAM in parallel is quite a common approach. You basically keep the old and new IAM running in parallel. As the user logs in, you authenticate it using the old IAM and register it using the new one. After a couple of months or so, you can get rid of the old IAM. For sure, there will be some users that haven’t logged in. For those, you could send them a reset password email.
And importing users is the most convenient one if you have the possibility.
Communities
The community of an IAM is extremely important, especially for open-source solutions.
You’ll encounter lots of problems and bugs along the way since it’s quite a complex thing to implement. And you’ll need to find answers to your existing problems and find best practices to avoid future ones.
Find large communities that are also active. It’s important to see a growing community because it means the solution is here to stay and will evolve in time.
Scalability
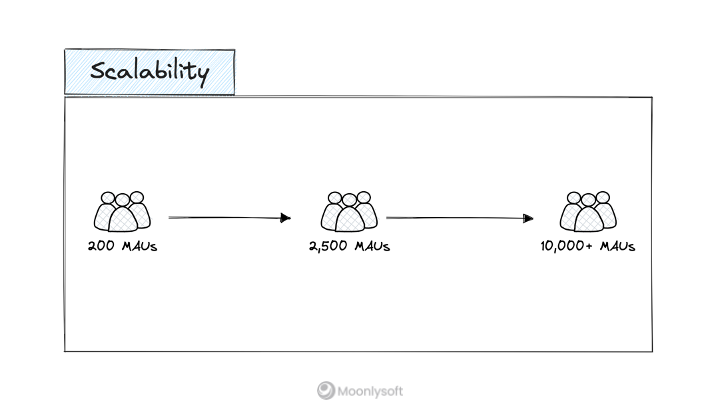
Scalability is an important factor when talking about IAM solutions and it’s especially important if your startup is focusing on B2C.
You can have 200 monthly active users in one month and easily scale it to 10,000+ in just a few months.
I’ve seen such growth over and over again. One good marketing campaign can get you there. But are you prepared for it?
Does your future IAM solution support this kind of growth?
There are some aspects you need to keep in mind related to scalability
- If you choose a Cloud dependent solution like Google Identity Platform, then you’ll benefit from a fairly low price, and autoscaling, but you’ll be dependent on their infrastructure.
- If you choose a solution like Auth0, then you might have a pricing issue.
I’ve heard so many stories where the startup grew exponentially overnight, and the price of their IAM grew so much that they had to migrate out of it.
- If you choose an open-source solution like Keycloak, then you’ll need a good strategy and plan for scaling the system. The worst thing that might happen to your app is a bottleneck at the authentication level.
Conclusion
There a lot of other criteria you should consider when choosing an IAM. We’ve presented what worked for us and what we’ve found to be valuable when evaluating a potential IAM for one of our clients.
I would recommend testing multiple solutions, creating proof of concepts, and being very delicate with this decision. Managing users is an extremely complex and fragile aspect of your application, so be sure you check all the boxes.